Innovative IT Solutions 621146771 employs a strategic framework to bolster its security measures. By integrating advanced encryption and cloud security, the organization seeks to safeguard sensitive data. Additionally, systematic risk assessments and vulnerability scans play a crucial role in identifying potential threats. This comprehensive approach not only enhances protection but also fosters trust among stakeholders. However, the effectiveness of these strategies raises important questions about their implementation and ongoing adaptability in an evolving threat landscape.
Understanding Innovative IT Solutions 621146771’s Security Approach
Innovative IT Solutions 621146771 adopts a multifaceted security approach that integrates cutting-edge technologies and best practices to safeguard digital assets.
This strategy relies on robust security frameworks and real-time threat intelligence, enabling proactive identification and mitigation of potential risks.
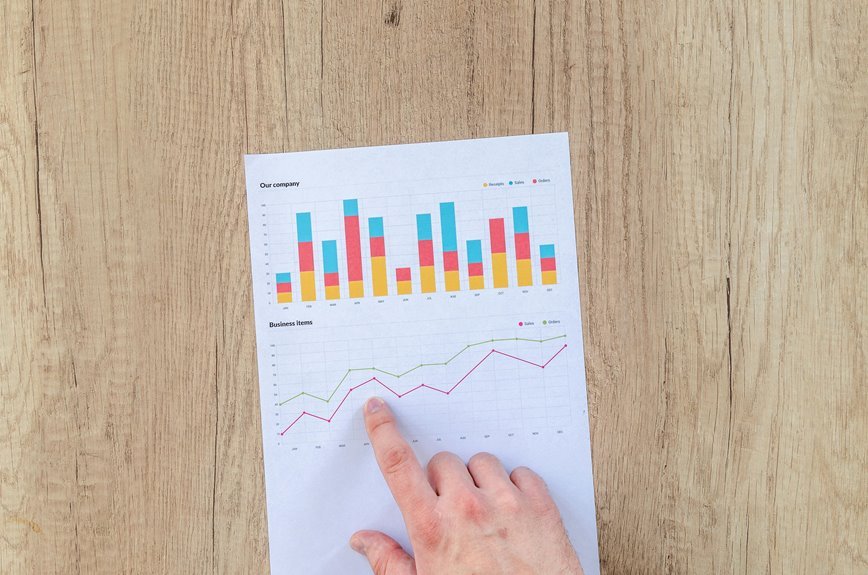
Key Technologies for Robust Data Protection
The security framework established by Innovative IT Solutions 621146771 sets the foundation for implementing key technologies that enhance data protection.
Central to this framework are advanced encryption techniques, which safeguard sensitive information against unauthorized access.
Additionally, robust cloud security measures ensure that data stored remotely remains protected from vulnerabilities, thereby enabling organizations to maintain operational integrity while fostering a secure digital environment conducive to freedom and innovation.
Comprehensive Risk Assessments: Identifying Vulnerabilities
Conducting comprehensive risk assessments is essential for organizations seeking to identify vulnerabilities within their IT infrastructure.
Through systematic vulnerability scanning, businesses can pinpoint weaknesses that may expose them to threats.
This proactive approach enables effective risk mitigation strategies, ensuring that potential security breaches are addressed before they escalate.
Ultimately, thorough assessments empower organizations to maintain robust defenses and safeguard their operational integrity.
Building Trust Through Effective Cybersecurity Strategies
Effective cybersecurity strategies are fundamental in fostering trust between organizations and their stakeholders.
By enhancing cybersecurity awareness, companies can inform stakeholders about their protective measures, thereby increasing confidence.
Utilizing trust metrics allows organizations to quantify their cybersecurity effectiveness, ensuring transparency.
This strategic alignment not only mitigates risks but also cultivates an environment where stakeholders feel secure, ultimately reinforcing their commitment to the organization.
Conclusion
In conclusion, Innovative IT Solutions 621146771 Security exemplifies a comprehensive approach to cybersecurity, merging advanced technologies with proactive risk management. Notably, studies indicate that organizations employing systematic vulnerability assessments can reduce security breaches by over 50%. This statistic underscores the importance of their commitment to identifying and addressing potential threats, ultimately fortifying their digital infrastructure. By fostering trust and operational integrity, Innovative IT Solutions not only protects sensitive data but also empowers organizational innovation and resilience in an evolving digital landscape.